#1 ON

PEER INSIGHTS
#1 ON

AI Agents
AI Agents
RiskProfiler aggregates intelligence across the internet. KnyX specialized agents triage, correlate, and map attack paths - then tell you the one fix that breaks the chain.
RiskProfiler aggregates intelligence across the internet. KnyX specialized agents triage, correlate, and map attack paths - then tell you the one fix that breaks the chain.



Trusted by 500+ enterprises
Global Firms
Global Firms
Gain trust and credibility with KnyX’s advanced reasoning layer, recognized by industry leaders for its clarity, accuracy, and ease of use.
Gain trust and credibility with KnyX’s advanced reasoning layer, recognized by industry leaders for its clarity, accuracy, and ease of use.

4.8/5
4.8/5

4.8 out of 5 stars
4.8 out of 5 stars

Best Ease of Use
2024
Too Many Alerts
Too Many Alerts
Cut through the noise and get clear, prioritized insights with KnyX’s intelligent reasoning layer
Cut through the noise and get clear, prioritized insights with KnyX’s intelligent reasoning layer
Breach alert at 2 AM again?
Too many tools, not enough visibility?
Is your SOC drowning in noise?
Lost track of critical assets?
Too many manual triage tasks?
Threat intel still siloed across teams?
Breach alert at 2 AM again?
Too many tools, not enough visibility?
Is your SOC drowning in noise?
Lost track of critical assets?
Too many manual triage tasks?
Threat intel still siloed across teams?
Meet Your
Meet Your
Agentic
KnyX Agentic
Team
Team
Transform complex threat data into clear, actionable insights with KnyX’s intelligent agents, empowering proactive security.
Transform complex threat data into clear, actionable insights with KnyX’s intelligent agents, empowering proactive security.
KnyX Intel
Understands public-cloud exposures.
KnyX Vendor
Tracks third parties and events.
KnyX Vendor
Tracks third parties and events.
KnyX Recon
KnyX Recon
OSINT-driven external asset discovery.
OSINT-driven external asset discovery.
KnyX Brand
KnyX Brand
Protects brand and customers from abuse.
Protects brand and customers from abuse.
+26 Agents
+26 Agents
KnyX Intel
Understands public-cloud exposures.
Comprehensive
Comprehensive
Use Cases
Use Cases
KnyX provides comprehensive solutions to safeguard your brand and detect risks, from fake domains to dark web threats.
KnyX provides comprehensive solutions to safeguard your brand and detect risks, from fake domains to dark web threats.

6/6
Trust Center
Trust Center
Trust Center
Controlled Evidence Sharing
Controlled Evidence Sharing
Controlled Evidence Sharing
Share pen test results, policies, and artifacts securely with relevant stakeholders with trackable, self-serve access.
Share pen test results, policies, and artifacts securely with relevant stakeholders with trackable, self-serve access.
Share pen test results, policies, and artifacts securely with relevant stakeholders with trackable, self-serve access.
Instant Trust Access
Instant Trust Access
Instant Trust Access
Streamlined NDA workflows and controlled security documentation access enables faster review and sales cycles.
Streamlined NDA workflows and controlled security documentation access enables faster review and sales cycles.
Streamlined NDA workflows and controlled security documentation access enables faster review and sales cycles.
Latest Insights
Stay informed with expert perspectives on cybersecurity, attack surface management,
and building digital resilience.
RiskProfiler :
RiskProfiler :
RiskProfiler offers the most complete feature set, including essential AI-driven tools that the competition simply misses.
RiskProfiler offers the most complete feature set, including essential AI-driven tools that the competition simply misses.

Others (Traditional Tools)
Others
Setup Time
Live in 30 minutes
Live in 30 minutes
Weeks-long setup
Weeks-long setup
Threat Intelligence
Agentic-AI risk engine
Agentic-AI risk engine
Static rule engines
Static rule engines
Attack Surface Discovery
Unified external-risk graph
Unified external-risk graph
Disconnected point tools
Disconnected point tools
Cloud Visibility
Cloud + internet view
Multi-cloud view
Partial asset mapping
Single cloud view
Vendor Risk Monitoring
Vendors + ratings built-in
Cloud + internet view
Separate VRM tools
Partial asset mapping
Questionnaires
AI vendor questionnaires
Vendors + ratings built-in
Manual spreadsheets
Manual vendor reviews
AI-assisted questionnaires
Separate VRM tools
AI vendor questionnaires
Manual spreadsheets
Impact-based risk scoring
Raw CVSS numbers
Digital + physical threats
Digital-only coverage
Built for MSSPs, mid-market
Enterprise-only focus
Dark web + brand
Separate DRP products
Brand & Digital Protection
Digital + physical threats
Digital-only coverage
Dark Web Coverage
Dark web + brand
Separate DRP products
Alerting Workflow
Real-time to Slack/Teams/Jira/ServiceNow, ownership & SLAs
Email digests; dashboard polling
Risk Prioritization
AI scoring + attack paths = fix what matters
Volume-driven alerts; low context
KnyX AI,
KnyX AI,
See exposures, map the path, and close risk—without drowning in noise.
See exposures, map the path, and close risk—without drowning in noise.
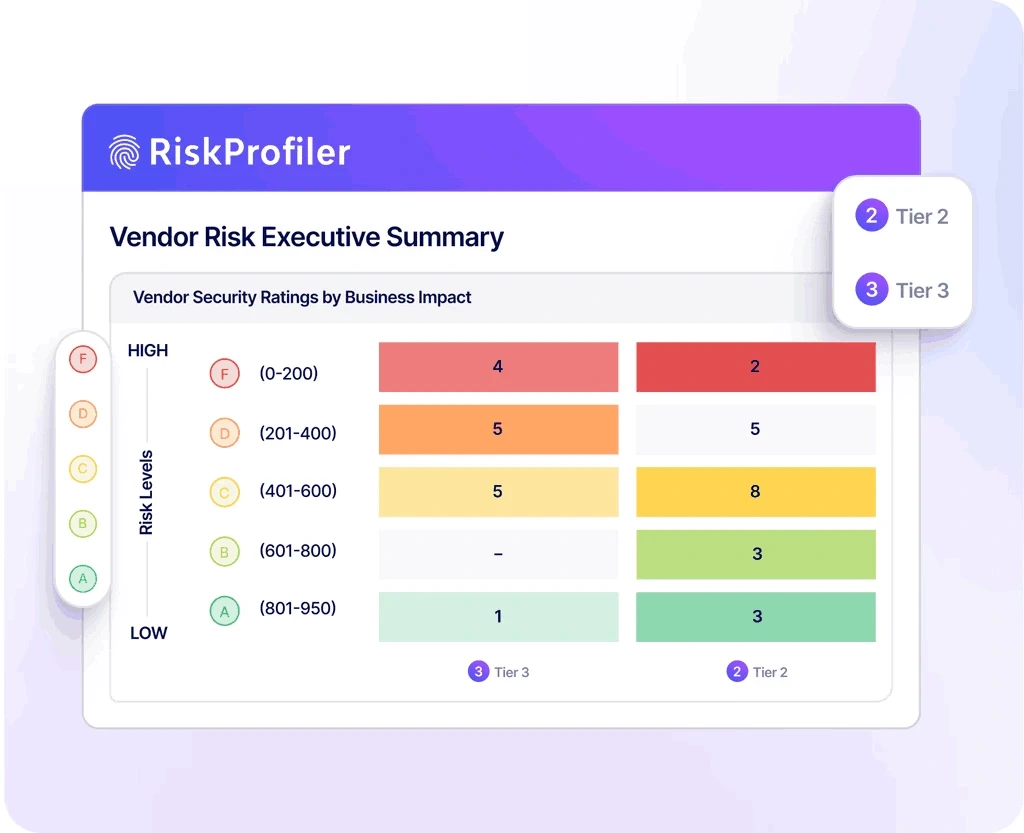
Vendor Risk
Correlation
Vendor Risk Correlation
No clear way to see how issues chain into real-world attack paths
No clear way to see how issues chain into real-world attack paths


Attack-Path
Analytics
Attack-Path Analytics
Certified security controls and processes
Certified security controls and processes


AI-Driven Prioritization
AI-Driven Prioritization
Scores by exploitability and impact
Scores by exploitability and impact

SOC2 & ISO27001 Compliant
SOC2 & ISO27001 Compliant
Certified security controls and processes
Certified security controls and processes

Security Leaders
Security Leaders
See what real users are saying about RiskProfiler - across
G2, Trustpilot, and X. We don't filter. We just ship.
See what real users are saying about RiskProfiler -across G2, Trustpilot, and X. We don't filter. We just ship.

4.8/5
4.8/5

4.8 out of 5 stars
4.8 out of 5 stars

Best Ease of Use
Best Ease of Use
2024
2024
It’s refreshing to have a platform that cuts through noise instead of adding more of it. RiskProfiler's unified insights have been consistently reliable and easy for the team to trust.

Leif Dreizler
Sr Engineering Manager, Semgrep
The shift from scattered alerts to a structured, contextual threat picture has been a big improvement. RiskProfiler's helped us skip the guesswork.

Travis McPeak
CEO Resourcely, Ex - Netflix & Databricks
RiskProfiler helped us keep up with breaches across our massive supply chain and cloud posture. Now, our team doesn't need to manually move through spreadsheets to find vendor security risks. It just gets done in minutes.

Lucas Nelson
Partner, Lytical Ventures
RiskProfiler not only shows us alerts, but it also communicates the problem it can cause and how. It shows how separate signals relate, which helps us move faster during investigations.

Nick Galbreath
GP at Aviso Ventures
RiskProfiler has made it easier to prioritize alerts with confidence. The platform’s correlation engine highlights the few issues that actually pose risk, not the dozens that look urgent but aren’t.

Andrew Peterson
GP at Aviso Ventures
RiskProfiler is a value-for-money tool. It’s fast, reduces overhead from multiple tools, and centralizes data for maximum efficiency—perfect for achieving meaningful outcomes quickly

Joe Schreiber
CEO, Appnovi
The unified dashboard has become an integral part of our security workflow. It’s straightforward, easy to use, and gives our analysts a clear view without the usual clutter. The best part is the platform scales as we need without any glitches or trouble.

Nikhil S.
Synack Red Team Legend
With RiskProfiler, noisy alerts drop off quickly. What’s left is a clean, reliable picture of the risks that truly matter. This clarity has transformed our workflow, driving efficiency and enhancing analyst productivity.

Praveen Nallasamy
Head of Product Security, BlackRock
The correlated insights and the attack path mapping of RiskProfiler are incredibly helpful. Instead of juggling separate tools, we now see exactly how issues connect across modules and can narrow down exactly where we need to focus.

Kelly Castriotta
Global Cyber Underwriting Officer, Markel
RiskProfiler gives us one unified platform to understand what’s happening across our entire threat surface. The contextual view takes a lot of guesswork out of prioritizing what to fix first.

Gary Merry
Board Member & Chief Growth Officer
It’s refreshing to have a platform that cuts through noise instead of adding more of it. RiskProfiler's unified insights have been consistently reliable and easy for the team to trust.

Leif Dreizler
Sr Engineering Manager, Semgrep
The shift from scattered alerts to a structured, contextual threat picture has been a big improvement. RiskProfiler's helped us skip the guesswork.

Travis McPeak
CEO Resourcely, Ex - Netflix & Databricks
RiskProfiler helped us keep up with breaches across our massive supply chain and cloud posture. Now, our team doesn't need to manually move through spreadsheets to find vendor security risks. It just gets done in minutes.

Lucas Nelson
Partner, Lytical Ventures
RiskProfiler not only shows us alerts, but it also communicates the problem it can cause and how. It shows how separate signals relate, which helps us move faster during investigations.

Nick Galbreath
GP at Aviso Ventures
RiskProfiler has made it easier to prioritize alerts with confidence. The platform’s correlation engine highlights the few issues that actually pose risk, not the dozens that look urgent but aren’t.

Andrew Peterson
GP at Aviso Ventures
RiskProfiler is a value-for-money tool. It’s fast, reduces overhead from multiple tools, and centralizes data for maximum efficiency—perfect for achieving meaningful outcomes quickly

Joe Schreiber
CEO, Appnovi
The unified dashboard has become an integral part of our security workflow. It’s straightforward, easy to use, and gives our analysts a clear view without the usual clutter. The best part is the platform scales as we need without any glitches or trouble.

Nikhil S.
Synack Red Team Legend
With RiskProfiler, noisy alerts drop off quickly. What’s left is a clean, reliable picture of the risks that truly matter. This clarity has transformed our workflow, driving efficiency and enhancing analyst productivity.

Praveen Nallasamy
Head of Product Security, BlackRock
The correlated insights and the attack path mapping of RiskProfiler are incredibly helpful. Instead of juggling separate tools, we now see exactly how issues connect across modules and can narrow down exactly where we need to focus.

Kelly Castriotta
Global Cyber Underwriting Officer, Markel
RiskProfiler gives us one unified platform to understand what’s happening across our entire threat surface. The contextual view takes a lot of guesswork out of prioritizing what to fix first.

Gary Merry
Board Member & Chief Growth Officer
We Have Answers!
We Have Answers!
Explore our FAQ to learn more about how RiskProfiler can help safeguard your digital assets and manage risks efficiently.
Explore our FAQ to learn more about how RiskProfiler can help safeguard your digital assets and manage risks efficiently.
What is the RiskProfiler external exposure management platform?
RiskProfiler is an agentic AI-powered external exposure management platform. It unifies external attack surface management, brand protection, dark web monitoring, cyber threat intelligence, vulnerability management, and third-party risk management into a single intelligence layer using its proprietary LLM engine, KnyX AI. The platform autonomously discovers external assets, correlates threat signals, validates evidence, and prioritizes remediation using attack-path context
How does RiskProfiler detect and prioritize external risks?
RiskProfiler uses autonomous discovery, intelligent correlation, and continuous monitoring to identify cloud exposures, vendor risks, leaked credentials, and brand abuse. KnyX AI correlates IoCs, threat actor chatter, CVEs, and asset data to map real-world attack paths, enabling AI-driven risk prioritization based on exploitability and business impact.
Who should use an AI-powered external threat intelligence platform?
An AI-powered external threat intelligence platform is designed for CISOs, SOC teams, MSSPs, and enterprises managing complex digital footprints. Organizations with cloud infrastructure, third-party vendors, customer-facing brands, and distributed assets use unified external threat intelligence to reduce alert fatigue and strengthen risk-based decision-making.
Does RiskProfiler integrate with existing security workflows?
RiskProfiler integrates with SIEM, SOAR, TIP, firewalls, ticketing systems, and custom applications to operationalize threat intelligence. It supports automated reporting, real-time alerts, takedown workflows, and trust center integrations, ensuring that external risk insights flow seamlessly into remediation and governance processes.
What makes RiskProfiler different from other cybersecurity platforms?
Unlike traditional solutions that address isolated risks, RiskProfiler provides unified external threat intelligence powered by agentic AI agents such as KnyX Cloud, KnyX Vendor, KnyX Recon, KnyX Brand, etc. It combines autonomous discovery, attack-path analytics, AI-based risk scoring, and continuous monitoring to transform fragmented alerts into prioritized, actionable security decisions.
Anticipate External Risks with KnyX AI
Discover how RiskProfiler’s AI agentic maps your external attack surface and exposes critical blind spots with a personalized demo.
Discover how RiskProfiler’s AI agentic maps your external attack surface and exposes critical blind spots with a personalized demo.
Book a Demo Today
Take a Product Tour
Take a Product Tour