Agentic AI-powered Cyber Threat Intelligence
Cyber Threat Intelligence,
Powered by KnyX Intel AI
Unified threat intelligence enriched with WHOIS, TLS, DNS, and paste data, mapped to MITRE ATT&CK to pinpoint threats across your external attack surface.

Trusted by 500+ enterprises
Recognized by
Industry Leaders

4.8/5

4.8 out of 5 stars

Best Ease of Use
2024
Your SOC’s
AI Security Assistant
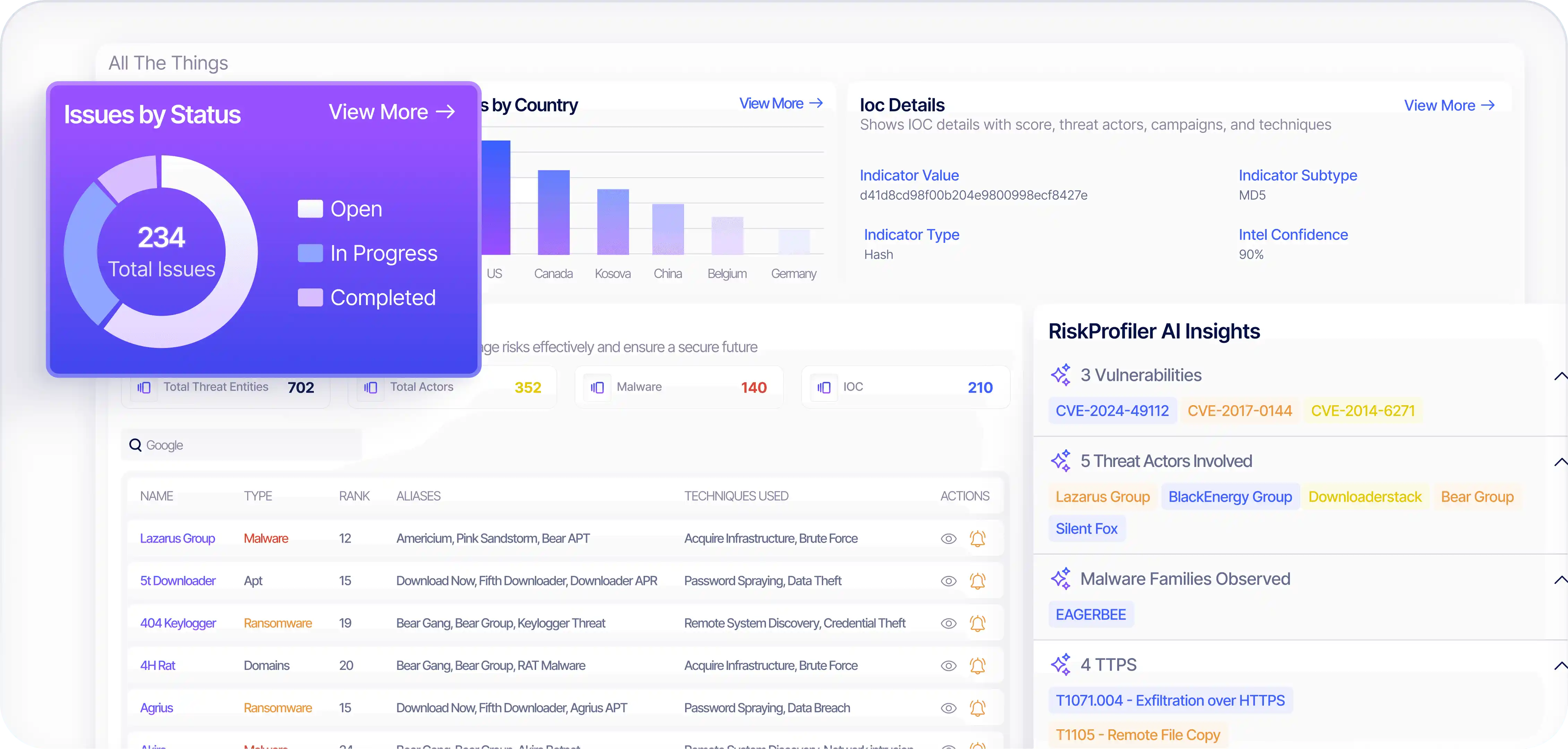
See Critical Threats, In Real-Time
From real-time IoCs to adversary patterns, KnyX Intel AI reveals risks across your digital footprint with unmatched precision, to help you stay ahead of emerging threat infrastructure.
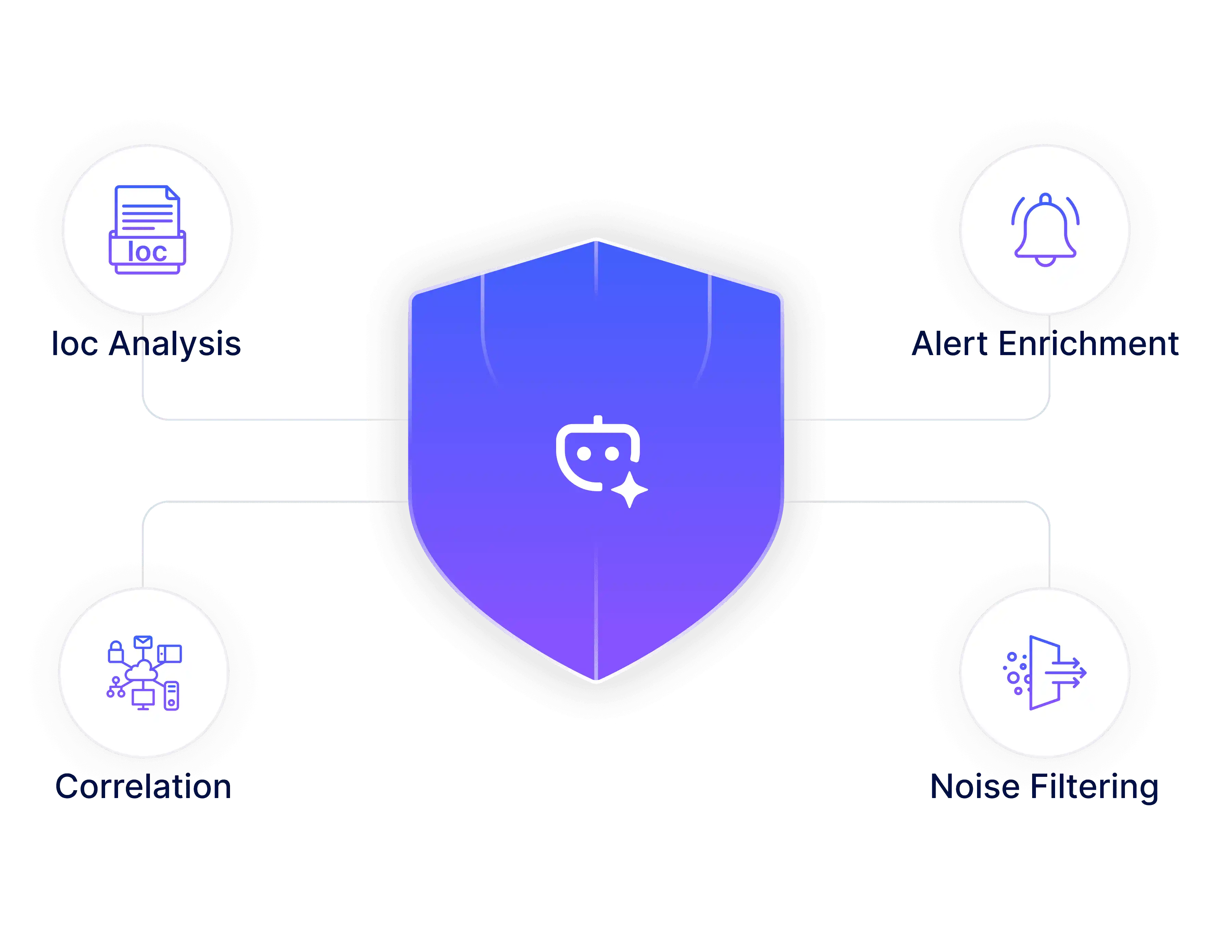
Automate SOC Workflows
RiskProfiler’s agentic AI automates IoC analysis, alert enrichment, correlation, and noise filtering, giving your analysts more time to focus on real incidents instead of repetitive manual triage.
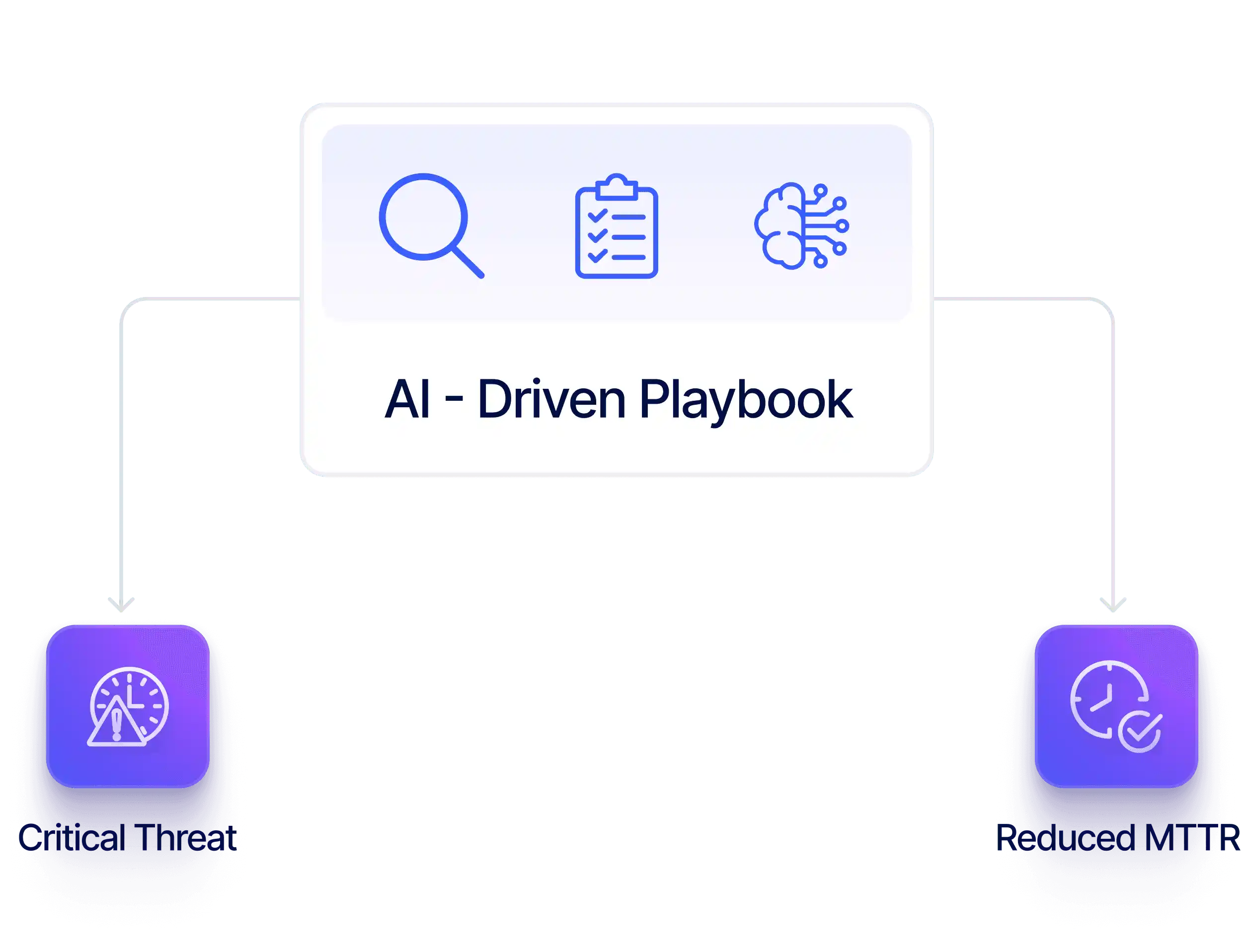
Reduce MTTR
Accelerate investigations with real-time context, AI-powered recommendations, and pre-approved playbooks, helping your SOC team reduce mean time to remediate (MTTR) for critical threats.
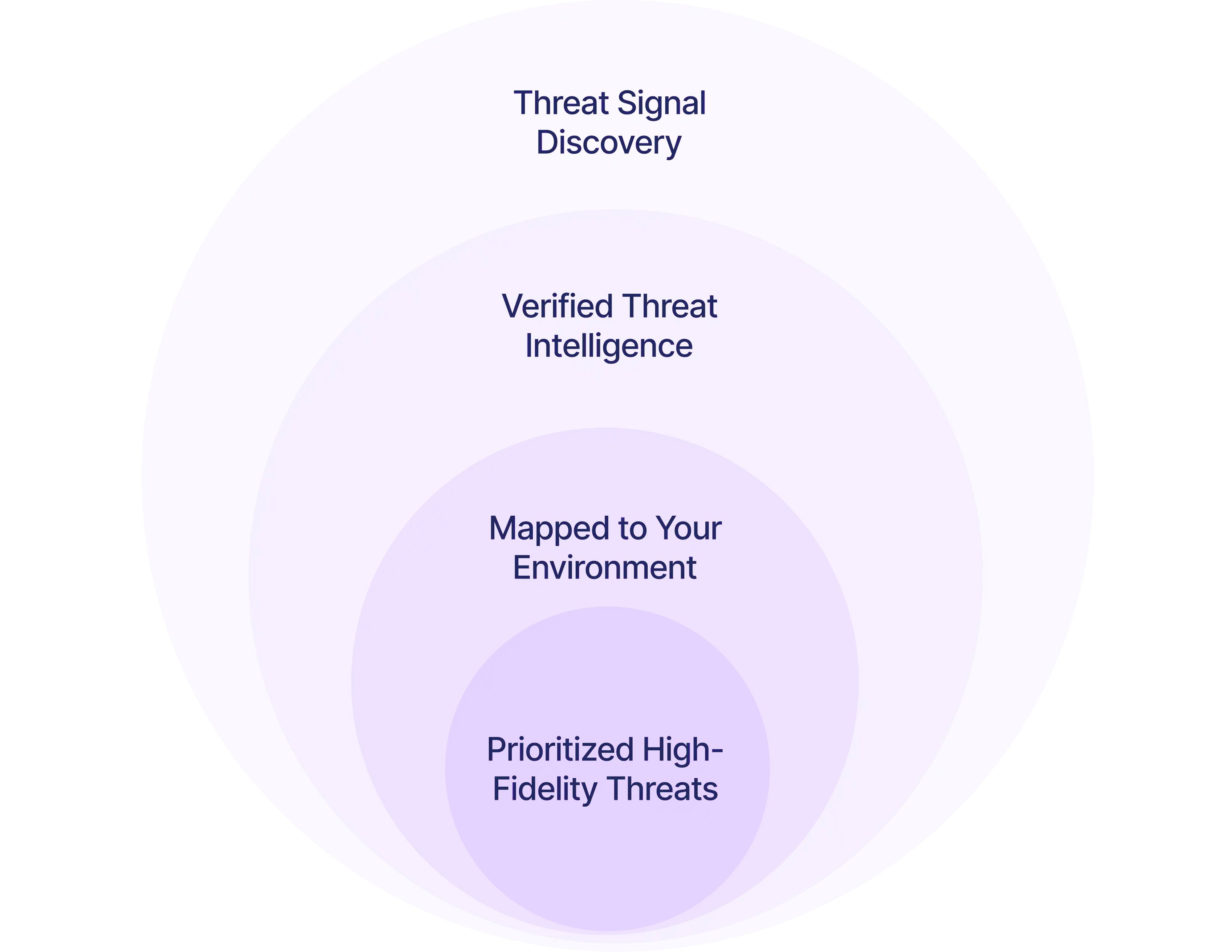
Proritize High-Fiedelity Risks
KnyX Intel AI highlights verified, high-impact threats mapped to your assets, cloud footprint, users, and vendors, ensuring your team always acts on what matters most.
How AI-Powered
Cyber
Threat Intelligence
Works
Bridge the gap between threat intelligence and your attack surface with KnyX AI, highlighting attacker intent, IoC relevance, and potential breaches.
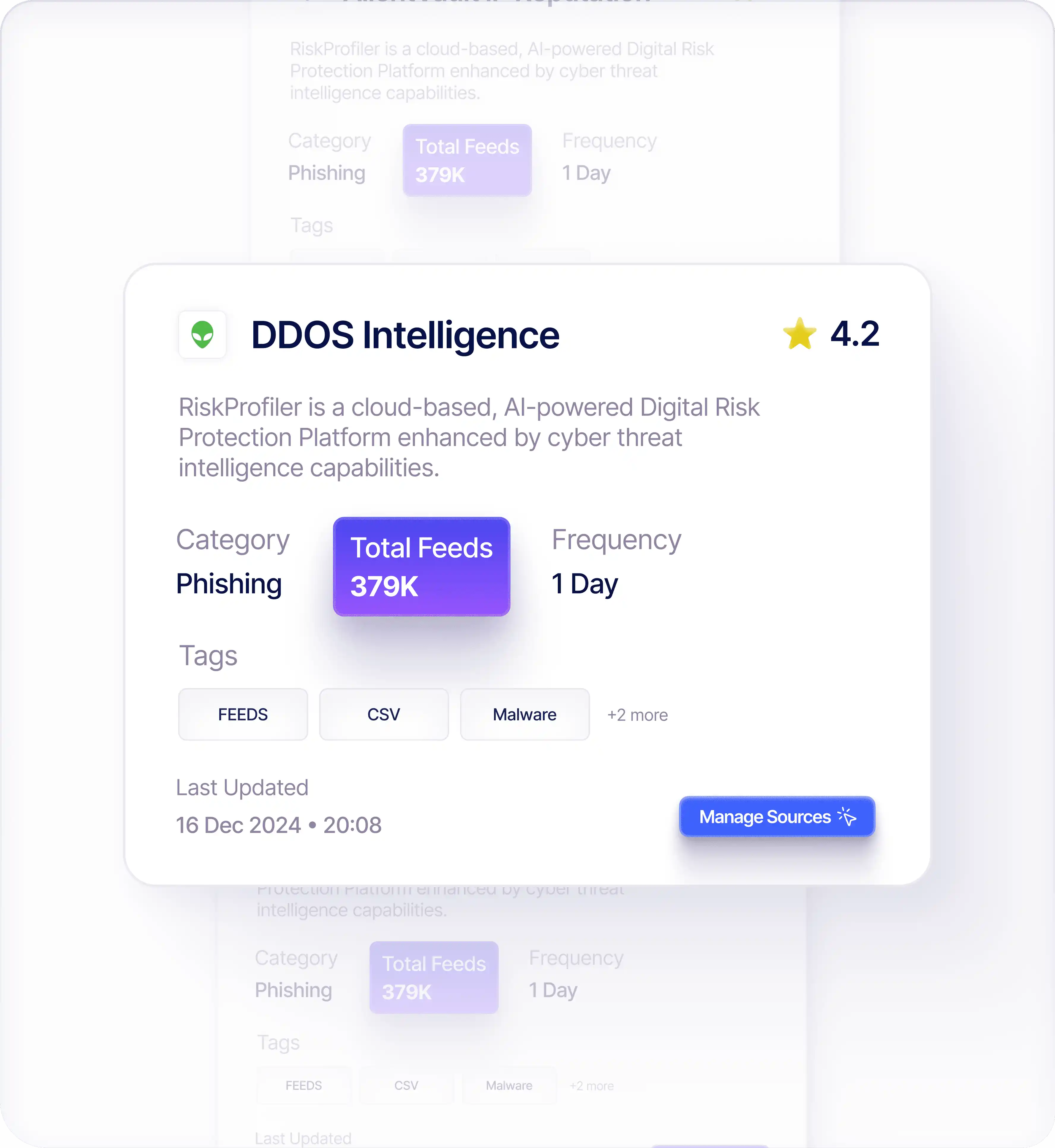
Identify Active Adversary Behavior & Malicious Kits
KnyX Intel AI continuously tracks malicious IPs, botnets, scanners, and exploit kits to curate attacker profiles actively probing vulnerabilities across your industry.
Map Prioritized IoCs to External Attack Surface
Surface high-confidence indicators linked to active exploitation, command-and-control infrastructure, and known attacker clusters so your team can act decisively.
Spot Potential Perimeter Breaches before Exploitation
Track early signals of compromise by identifying malicious IP scanning ports, probing services, or testing credentials, allowing SOC teams to investigate threats before they become incidents.
Turn
Cyber Threat Intelligence
Into Confident Security Decisions
RiskProfiler delivers real-time IoC detection, actor insight, and contextual validation, enabling your team to respond faster, prioritize accurately, and prevent attacks before they impact the business.
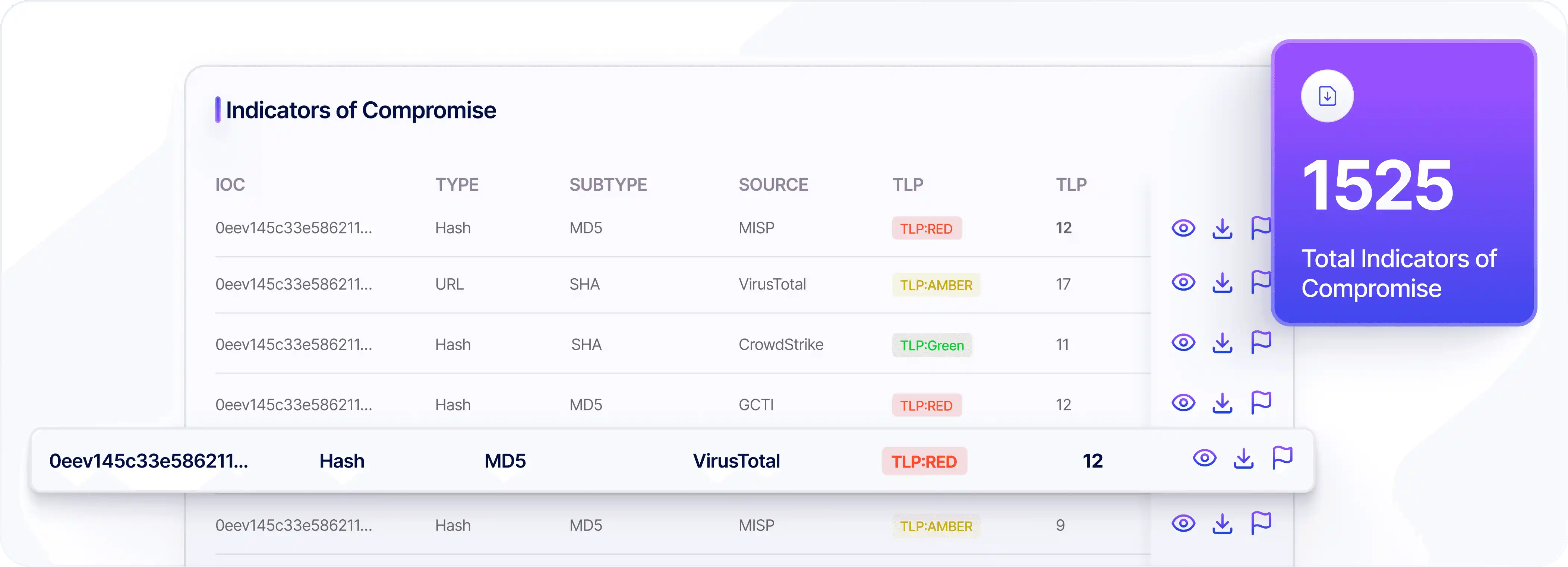
Receive Live IoC & Exposure Updates
Stay ahead of cyber adversaries by identifying critical threats based on active exploitation patterns and Indicators of Compromise (IoC) impacting your environment.
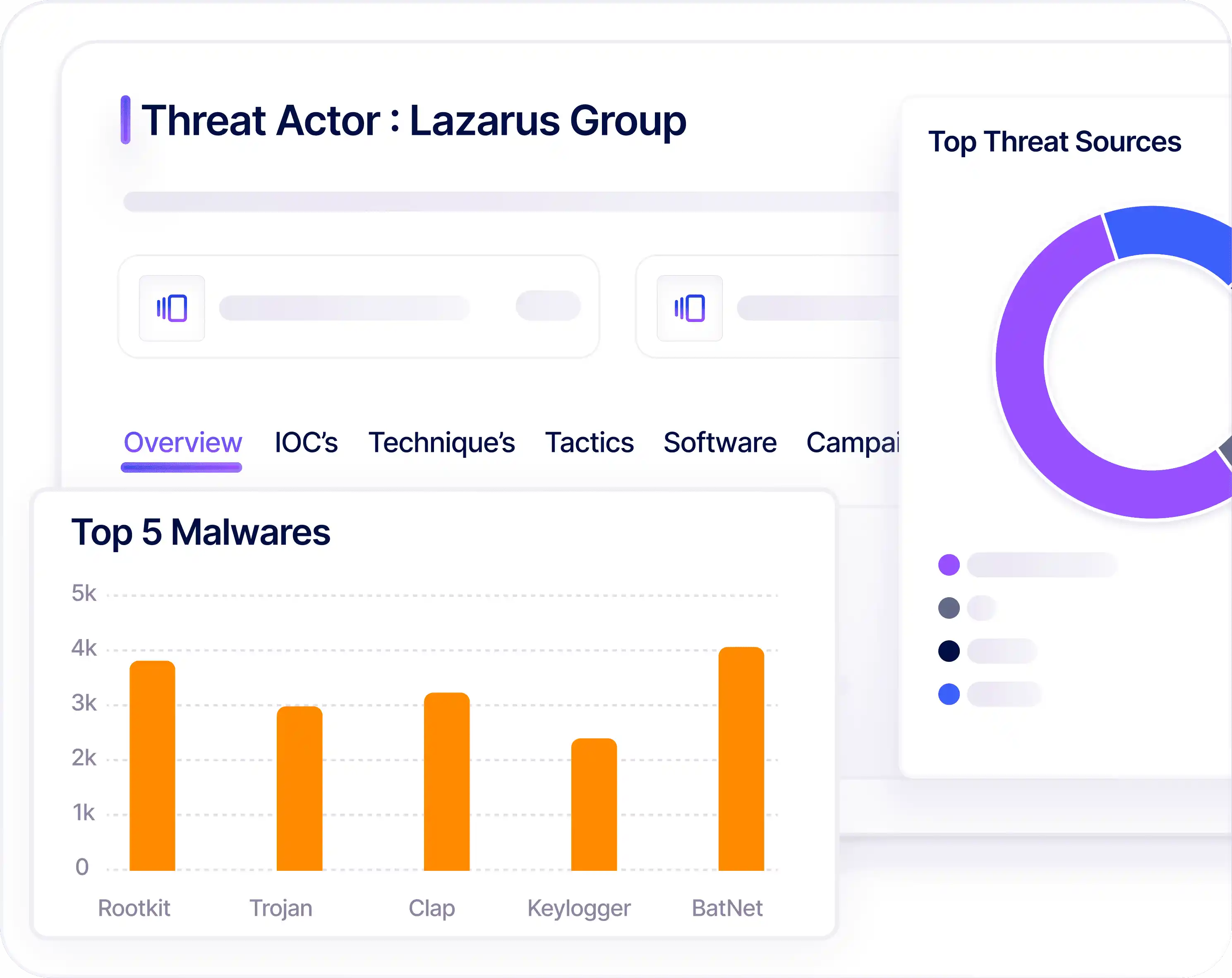
Adversary Attribution
Agentic AI links threats to attacker groups, tools, and malware, clarifying intent, strategy, and likely actions.
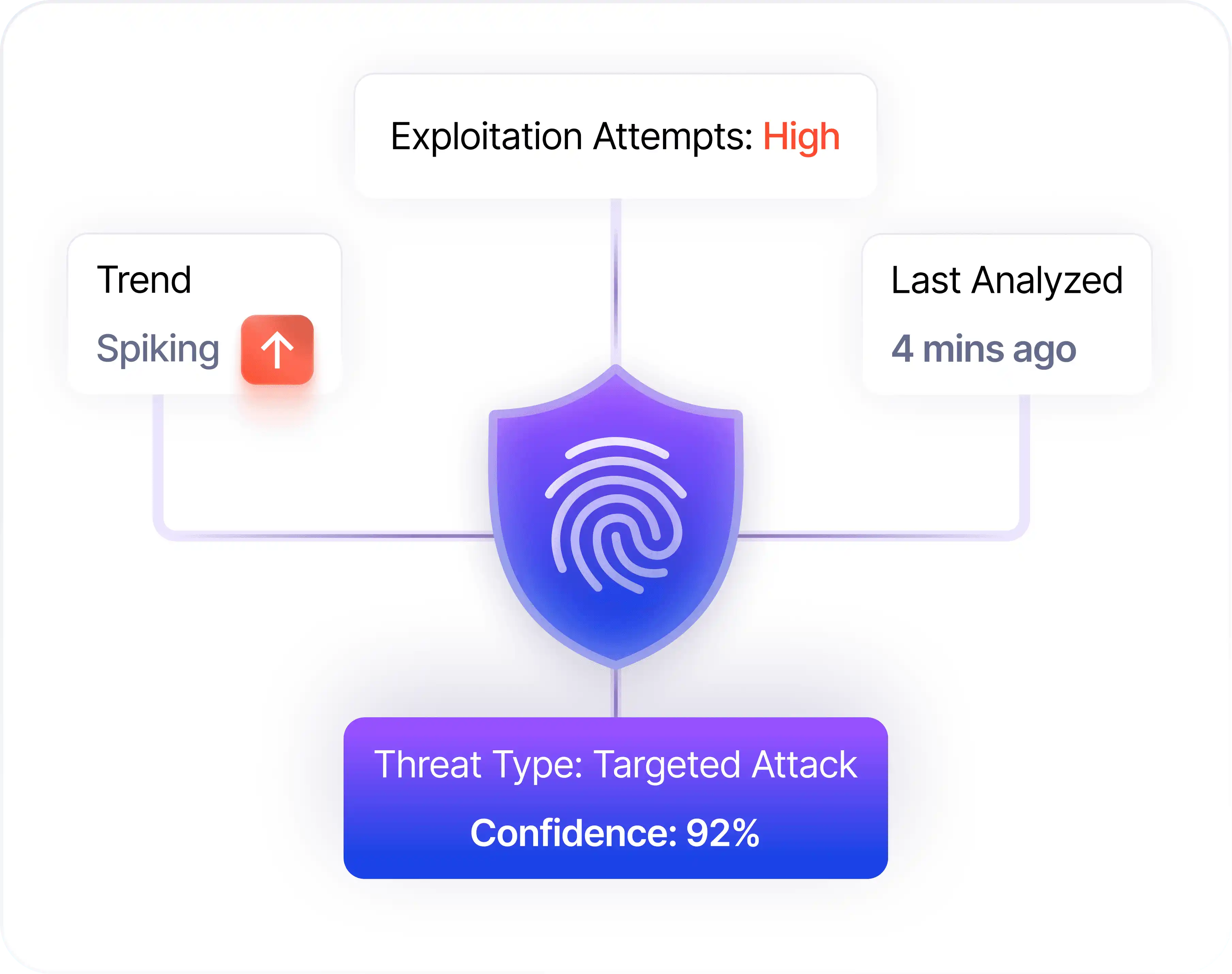
Contextual Threat Validation
KnyX Intel AI helps teams determine whether a threat is part of broad, opportunistic scanning or a focused attempt against your assets by analyzing trends.
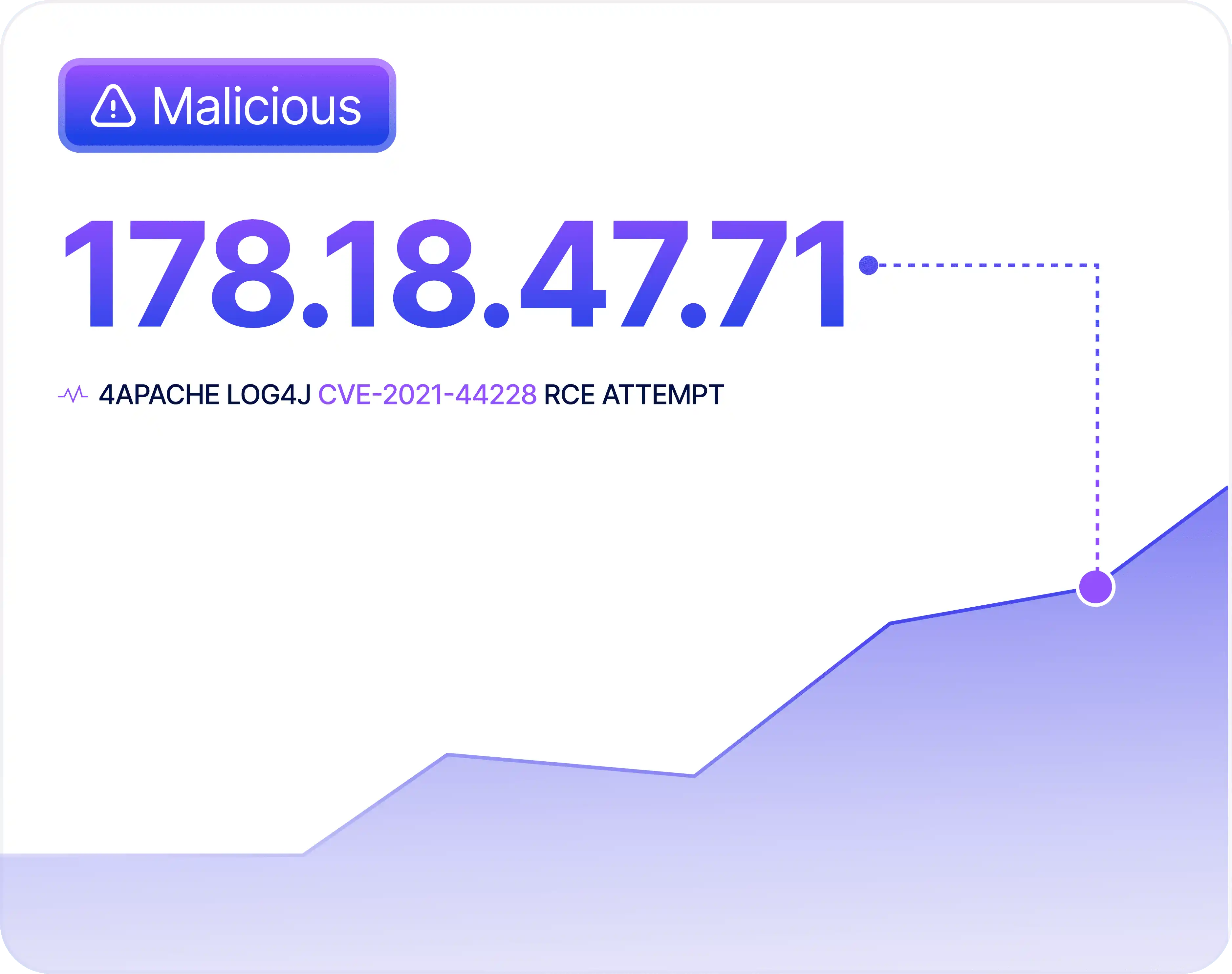
Block Malicious Scanners
Block malicious IPs probing for vulnerabilities autonomously, reducing the risk of mass scanning or unauthorized access attempts across your systems.
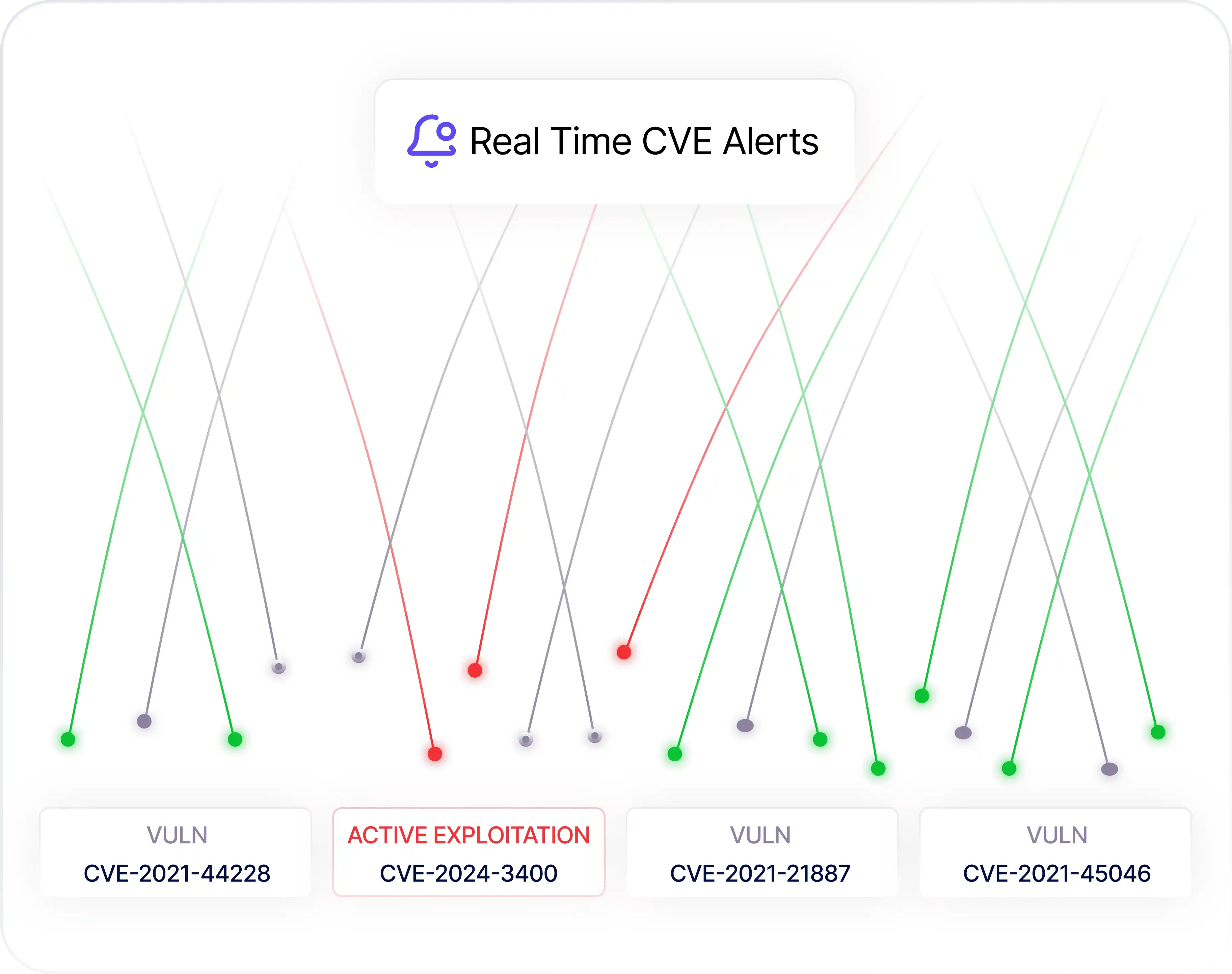
Alerts for CVEs & Exploitation
Receive instantaneous alerts when any known CVE is actively exploited, enabling faster patching or mitigation to prevent breaches and contain impact before escalation.
Integrated
SOC
Intelligence
Request cyber threat intelligence on threats, exposures, and adversary behavior, helping analysts move from questions to answers in seconds.
Retrieve CVE insight on active exploitation patterns and attacker interest
Uncover exposure risks tied to active attacker behavior
Request detailed profiles of threat groups shaping current campaigns
Book a Demo

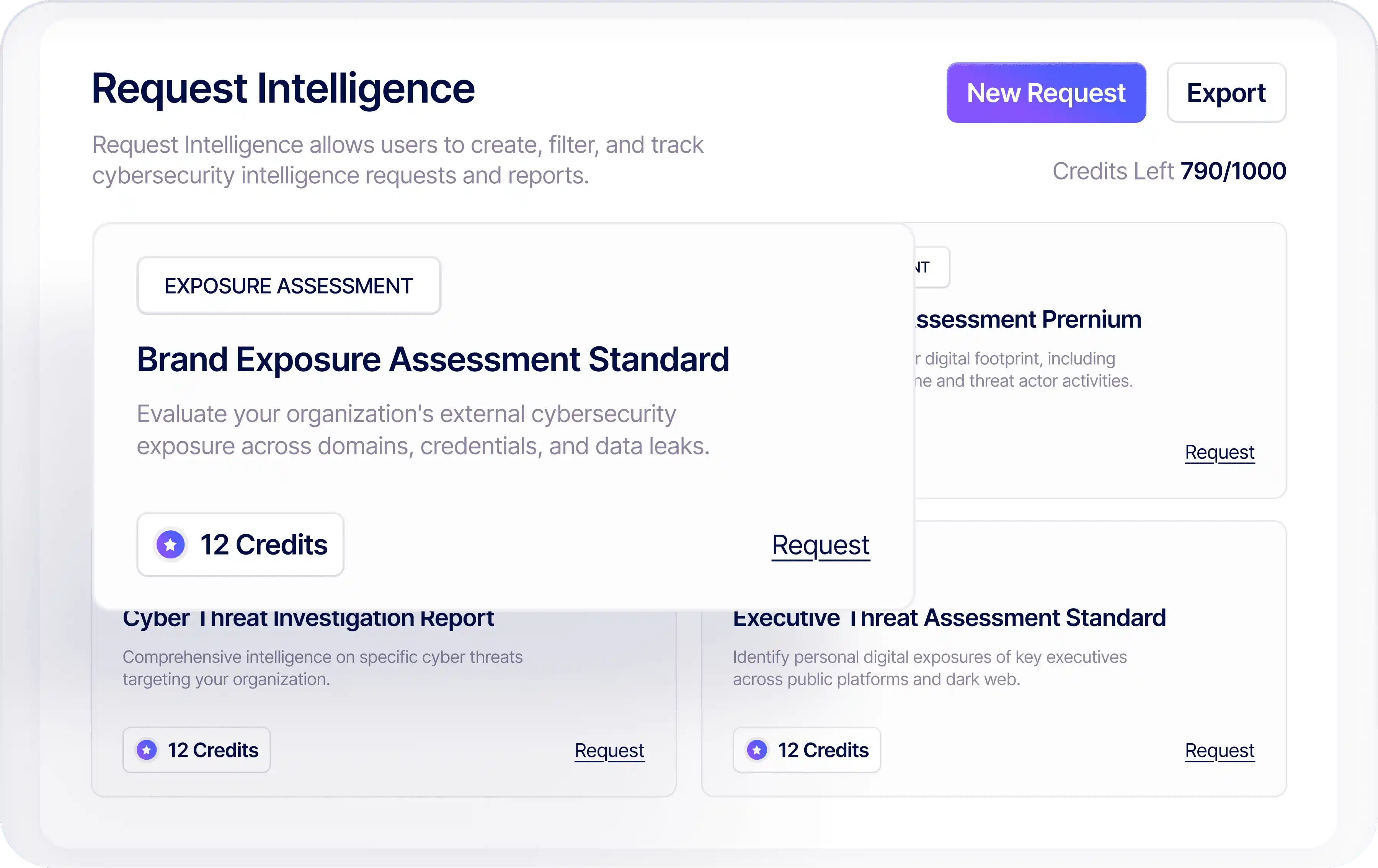
On-Demand
Threat Insights
Request cyber threat intelligence on threats, exposures, and adversary behavior, helping analysts move from questions to answers in seconds.
Retrieve CVE insight on active exploitation patterns and attacker interest
Uncover exposure risks tied to active attacker behavior
Request detailed profiles of threat groups shaping current campaigns
Book a Demo
Benefits of RiskProfiler
Cyber Threat Intelligence
Stay vigilant across your external digital ecosystem 24X7 with proactive cyber threat intelligence.

Enhanced SOC Efficiency
Accelerate triaging with enriched alerts that highlight the critical threat signals, improving the efficiency and productivity of your SOC teams.

Reduce False Positives
Increase detection confidence with contextualized AI-powered insights, which correlates potential threats, reducing false positives.

Seamless Investigation Workflow
Streamline investigations by integrating real-time threat intelligence into your existing SOAR/SIEM workflows, accelerating response times.
Integrated Threat Hunting
Transform threat hunting from guesswork into guided analysis with contextual intelligence that highlights meaningful adversary activity.
What
Security Leaders
About RiskProfiler CTI

4.8/5

4.8 out of 5 stars

Best Ease of Use
2024
It’s refreshing to have a platform that cuts through noise instead of adding more of it. RiskProfiler's unified insights have been consistently reliable and easy for the team to trust.

Leif Dreizler
Sr Engineering Manager, Semgrep
The shift from scattered alerts to a structured, contextual threat picture has been a big improvement. RiskProfiler's helped us skip the guesswork.

Travis McPeak
CEO Resourcely, Ex - Netflix & Databricks
RiskProfiler helped us keep up with breaches across our massive supply chain and cloud posture. Now, our team doesn't need to manually move through spreadsheets to find vendor security risks. It just gets done in minutes.

Lucas Nelson
Partner, Lytical Ventures
RiskProfiler not only shows us alerts, but it also communicates the problem it can cause and how. It shows how separate signals relate, which helps us move faster during investigations.

Nick Galbreath
GP at Aviso Ventures
RiskProfiler has made it easier to prioritize alerts with confidence. The platform’s correlation engine highlights the few issues that actually pose risk, not the dozens that look urgent but aren’t.

Andrew Peterson
GP at Aviso Ventures
RiskProfiler is a value-for-money tool. It’s fast, reduces overhead from multiple tools, and centralizes data for maximum efficiency—perfect for achieving meaningful outcomes quickly

Joe Schreiber
CEO, Appnovi
The unified dashboard has become an integral part of our security workflow. It’s straightforward, easy to use, and gives our analysts a clear view without the usual clutter. The best part is the platform scales as we need without any glitches or trouble.

Nikhil S.
Synack Red Team Legend
With RiskProfiler, noisy alerts drop off quickly. What’s left is a clean, reliable picture of the risks that truly matter. This clarity has transformed our workflow, driving efficiency and enhancing analyst productivity.

Praveen Nallasamy
Head of Product Security, BlackRock
The correlated insights and the attack path mapping of RiskProfiler are incredibly helpful. Instead of juggling separate tools, we now see exactly how issues connect across modules and can narrow down exactly where we need to focus.

Kelly Castriotta
Global Cyber Underwriting Officer, Markel
RiskProfiler gives us one unified platform to understand what’s happening across our entire threat surface. The contextual view takes a lot of guesswork out of prioritizing what to fix first.

Gary Merry
Board Member & Chief Growth Officer

Ready to Accelerate Your Cyber Threat Management?
Join hundreds of security teams who trust KnyX Intel AI to cut through the noise and focus on what matters most.
Latest Insights
Stay informed with expert perspectives on cybersecurity, attack surface management,
and building digital resilience.
Curious About AI Threat Intelligence?
Let Us Break It Down.
Get clear answers on how KnyX Intel AI enhances detection accuracy, reduces noise, and uncovers threats before attackers strike.
What is the RiskProfiler Cyber Threat Intelligence platform?
RiskProfiler Cyber Threat Intelligence is an agentic AI-powered CTI platform powered by KnyX Intel AI that turns raw threat feeds into actionable intelligence. It enriches indicators using WHOIS, TLS, DNS, and paste-source context, then maps threats to MITRE ATT&CK for faster triage. This helps security teams validate relevance, prioritize high-confidence threats, and guide response across the external attack surface.
How does AI-powered cyber threat intelligence reduce false positives?
KnyX Intel AI correlates IoCs from multiple sources, validates attacker intent, and maps threats directly to your environment. By enriching SIEM alerts with adversary attribution, CVE exploitation context, and campaign data, it filters noise and highlights high-fidelity threats. This improves detection confidence and accelerates SOC triage and response workflows.
Who should use agentic AI-powered cyber threat intelligence?
Agentic AI-driven cyber threat intelligence is designed for SOC teams, threat hunters, and security operations leaders managing complex digital ecosystems. Organizations seeking real-time IoC detection, adversary infrastructure tracking, and proactive perimeter breach identification benefit from CTI software that integrates directly into incident response and threat hunting workflows.
Does RiskProfiler CTI integrate with SIEM and SOAR tools?
RiskProfiler Cyber Threat Intelligence integrates with SIEM, SOAR, ticketing, IAM, and communication platforms such as Slack, Jira, and ServiceNow. It enriches alerts with attacker context, triggers automated playbooks based on high-confidence intelligence signals, and streamlines coordinated response across existing security stacks.
What makes RiskProfiler different from traditional threat intelligence tools?
Unlike traditional threat intelligence tools that provide static feeds, RiskProfiler uses agentic AI to continuously correlate live IoCs, CVEs, and adversary behavior with your assets. It maps threats to MITRE ATT&CK, validates contextual relevance, and delivers prioritized, environment-specific intelligence that supports faster, more confident security decisions.
Schedule a Live
AI-
Powered
Threat
Intelligence Demo
In a 30-minute session, see how RiskProfiler correlates threat activity across external sources, enriches attacker context, and prioritizes the signals that matter most.
Threat signal correlation and risk scoring
Adversary infrastructure and exposure insights
Clearer, faster security prioritization

4.8/5

4.8 out of 5 stars

Best Ease of Use
2024
Take a Product Tour
Agentic AI-powered Cyber Threat Intelligence
Cyber Threat Intelligence,
by
KnyX Intel AI
Unified threat intelligence enriched with WHOIS, TLS, and DNS data — extended across dark web and paste sites, mapped to MITRE ATT&CK for precision containment.


Trusted by 500+ enterprises
Trusted by
Industry Leaders

4.8/5


4.8 out of 5 stars
KnyX Intel AI reveals risks across your footprint with real-time IOCs and adversary patterns.
Instant Threat Detection
Your SOC’s
AI Security
See Critical Threats,
Assistant
In Real-Time
Automate SOC Workflows
Agentic AI automates IOC analysis and noise filtering so analysts focus on real incidents.
Threat Data
Incident Detection
Noise Filtering
IOC Analysis




Reduce MTTR
Accelerate incident resolution with AI-driven analysis that cuts noise and surfaces real threats instantly.
Instant Insights
Quick Remediation
Efficient Workflows
Rapid Triage
Proritize High-Fiedelity Risks
Identify and elevate the most critical, high-confidence threats so your team focuses on what truly matters.
Critical Threat Focus
High-Signal Alerts
Priority Scoring
Threat Prioritization


Step 2
Contextual Threat Validation
Verify threats in context to reduce false positives and improve response accuracy.


Step 3
Receive Live IoC & Exposure Updates
Identify critical threats by tracking active exploits and IoCs impacting your environment.


Step 1
Block Malicious Scanners
Autonomously block malicious IPs to stop scans and unauthorized access attempts.


Smart Threat Insight
Why is
Cyber Threat
Important for
Intelligence
Your Business?
KnyX Intel AI reveals risks across your footprint with real-time IOCs and adversary patterns.


Unified SOC Intelligence
Control Access
Share
with Confidence
Govern Trust Center sharing with secure links, public profiles, and partner distribution.
Reduce False Positives
Boost team productivity with automated workflows and intelligent data processing.
Enhanced SOC Efficiency
Minimize noise and focus on real threats with advanced filtering and validation.
Seamless Investigation Workflow
Accelerate incident response by integrating tools for smooth, collaborative analysis.
Integrated Threat Hunting
Continuously hunt for threats across your environment with automated, proactive detection.


Proactive Cyber Intelligence
Benefits of RiskProfiler
Cyber Threat Intelligence
Stay vigilant across your external digital ecosystem 24X7 with proactive threat intelligence.
Security Leaders
See what real users are saying about RiskProfiler. We don't filter. We just ship.

4.8/5


4.8 out of 5 stars
It’s refreshing to have a platform that cuts through noise instead of adding more of it. RiskProfiler's unified insights have been consistently reliable and easy for the team to trust.

Leif Dreizler
Sr Engineering Manager, Semgrep
The shift from scattered alerts to a structured, contextual threat picture has been a big improvement. RiskProfiler's helped us skip the guesswork.

Travis McPeak
CEO Resourcely, Ex - Netflix & Databricks
RiskProfiler helped us keep up with breaches across our massive supply chain and cloud posture. Now, our team doesn't need to manually move through spreadsheets to find vendor security risks. It just gets done in minutes.

Lucas Nelson
Partner, Lytical Ventures
RiskProfiler not only shows us alerts, but it also communicates the problem it can cause and how. It shows how separate signals relate, which helps us move faster during investigations.

Nick Galbreath
GP at Aviso Ventures
RiskProfiler has made it easier to prioritize alerts with confidence. The platform’s correlation engine highlights the few issues that actually pose risk, not the dozens that look urgent but aren’t.

Andrew Peterson
GP at Aviso Ventures
RiskProfiler is a value-for-money tool. It’s fast, reduces overhead from multiple tools, and centralizes data for maximum efficiency—perfect for achieving meaningful outcomes quickly

Joe Schreiber
CEO, Appnovi
The unified dashboard has become an integral part of our security workflow. It’s straightforward, easy to use, and gives our analysts a clear view without the usual clutter. The best part is the platform scales as we need without any glitches or trouble.

Nikhil S.
Synack Red Team Legend
With RiskProfiler, noisy alerts drop off quickly. What’s left is a clean, reliable picture of the risks that truly matter. This clarity has transformed our workflow, driving efficiency and enhancing analyst productivity.

Praveen Nallasamy
Head of Product Security, BlackRock
The correlated insights and the attack path mapping of RiskProfiler are incredibly helpful. Instead of juggling separate tools, we now see exactly how issues connect across modules and can narrow down exactly where we need to focus.

Kelly Castriotta
Global Cyber Underwriting Officer, Markel
RiskProfiler gives us one unified platform to understand what’s happening across our entire threat surface. The contextual view takes a lot of guesswork out of prioritizing what to fix first.

Gary Merry
Board Member & Chief Growth Officer
Voices of Security Leaders
Ready to Transform
Your Threat Management
Join hundreds of security teams who trust KnyX to cut through the noise and focus on what matters most.
Book a Demo Today
Subscribe to our Newsletter
By submitting your email address, you agree to receive RiskProfiler’s monthly newsletter. For more information, please read our privacy policy. You can always withdraw your consent.